BootHole vulnerability threatens Windows and Linux computers
It may have a rather amusing name but this new security vulnerability is no laughing matter. Researchers have discovered a bug in software that runs even before any operating system starts up that could grant hackers unbridled access to a computer. And while Linux computers are directly at risk from this BootHole exploit, almost all Windows computers from the past decade or so are also vulnerable to getting hijacked and hacked with almost no telltale signs of a compromised system.
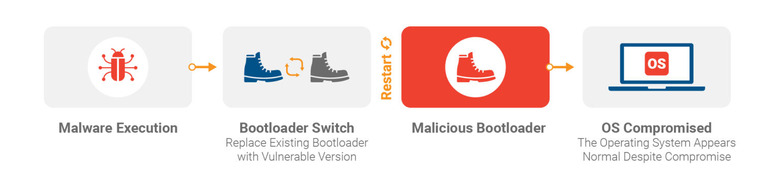
At the heart of this vulnerability is the process of booting up a computer and the UEFI Secure Boot system that should be protecting that process. Whether it's a PC or even a phone, there is a piece of software called a bootloader that manages the startup of the operating system itself or any recovery mode that may need to be run. To protect that bootloader, the UEFI Secure Boot system was developed as a way to vet legit bootloaders and firmware while blacklisting known bad ones.
The problem occurs when the bootloader itself has a bug that could be exploited to gain privileged access to an otherwise secure system, as in the case with the GRUB2 bootloader used by almost all Linux distributions. A bootloader runs with more privilege than an operating system's root or admin user and its only verification happens via signed or certified code. If a hacker is able to swap a bootloader with a valid but exploitable version, the Secure Boot process would be none the wiser.
Unfortunately, BootHole doesn't affect Linux systems only. Because managing certificates for every firmware, driver, or bootloader is a logistics nightmare, the computer industry has settled on using a certificate authority or CA for signing those pieces of software, of which Microsoft's 3rd Party UEFI CA is the most popular. Since that UEFI CA considers GRUB2 to be a certified bootloader, any computer that trusts Microsoft's 3rd Party UEFI CA are also vulnerable to BootHole, which means almost all computers currently in the market from the past few years.
The security researchers at Eclypsium who reported the vulnerability are calling for an industry-wide update and re-signing of affected software, something it admits could take years to happen. It isn't, however, reason to panic as there are small steps that can be taken to protect one's computer until all the permanent fixes are in place.
Those mitigations include installing related security updates that OEMs and Linux distributions have not rolled out. It also means becoming extra careful about running unknown programs with privileged access, as that will be the only way a hacker can swap out a secure GRUB2 bootloader for a vulnerable one. Admittedly, that's harder to pull off on Linux than on Windows but that shouldn't be a reason to be lax.