AT&T Caught Injecting Extra Ads On Airport WiFi Hotspot
It seems AT&T may be tampering with mobile users' internet traffic for their own benefit on their "free" public WiFi hotspots. The company's hotspot at the Dulles International Airport in Virginia was found to be using ad-injecting code to deliver more advertisements to users while they browse the web. Stanford lawyer and computer scientist Jonathan Mayer made the discovery, detailing the tactic on his blog Web Policy.
In addition to finding extra ads on websites that are already ad-supported, such as The Wall Street Journal, Mayer was seeing advertising on educational and government websites, including those for Stanford and even the FCC, where there shouldn't be such sponsorship. After analyzing the web source, he found the WiFi network was adding code that modified his traffic and pulled promotions from other sources.
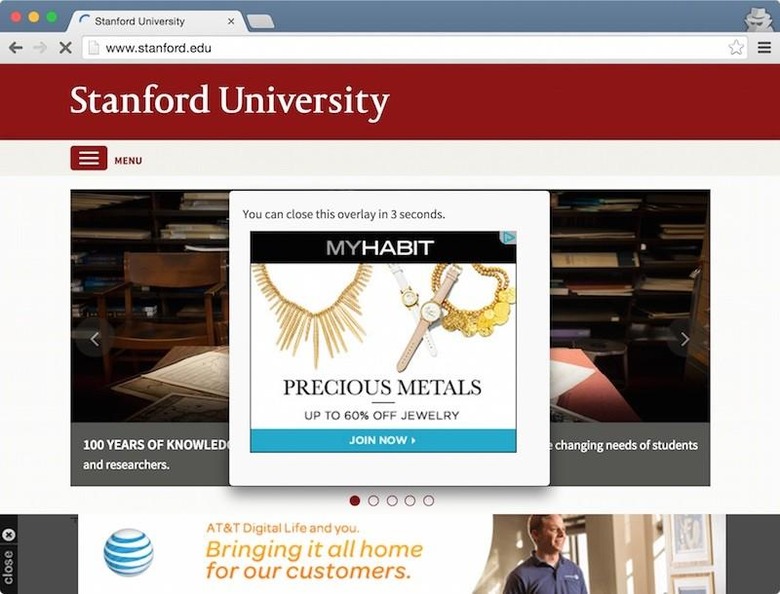
In his blog post, Mayer details the three changes the code was making: adding a stylesheet for advertising, injecting an extra advertisement for browsers that didn't JavaScript, and running two more scripts that controlled ad loading and display. This is how the platform was able to import and display third-party ads.
AT&T's terms of service for the public WiFi have no direct mention of displaying additional advertising or the use of such a platform. Mayer notes that not only do the ads slow down users' browsing and making web pages look awful, but the ad-injecting poses a security risk, as web developers haven't designed their sites for extra scripts to be run.
A year ago, Comcast was found doing the same thing on millions of their public WiFi hotspots. In theory, this practice is restricted according to the FCC's rules on net neutrality and other legislation, but it's still in a legal gray area, and a number of other companies have done the same following the Comcast discovery.
Update: An AT&T spokesperson gave us the following statement:
"Our industry is constantly looking to strike a balance between the experience and economics of free Wi-Fi. We trialed an advertising program for a limited time in two airports (Dulles and Reagan National) and the trial has ended. The trial was part of an ongoing effort to explore alternate ways to deliver a free Wi-Fi service that is safe, secure and fast."
SOURCE Web Policy
