Android Malware Agent Smith Replaces Legit Apps With Infected Copies
It's not uncommon to hear of some form of Android malware wreaking havoc on users' lives. Some of these even manage to get into Google Play Store, much to the platform maker's shame. This new strain of virus at least doesn't come from Android's canonical app store but its effects are no less destructive. In fact, it can manage to replace apps you did install from Google Play Store with infected duplicates, which is why its discoverers have dubbed it "Agent Smith".
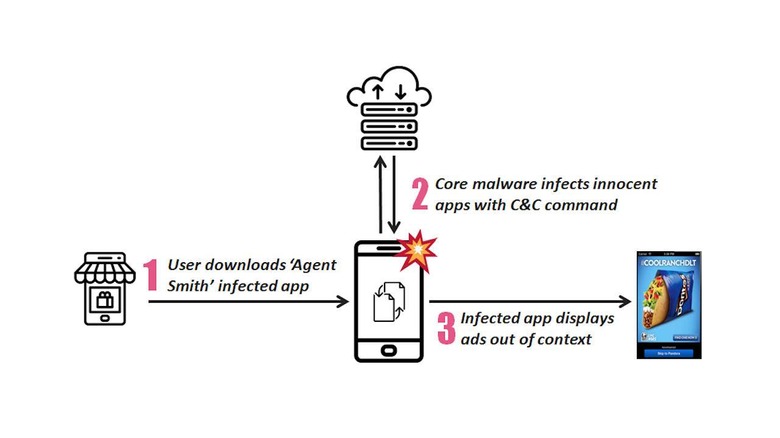
The malware is both fascinating and frightening at the same time because of this. Security researchers from Check Point have identified that the malware works in three stages. The first involves checking if the phone has installed apps that are on its "hit list" while the second stage in actually installs the malware without user intervention, much less knowledge.
The third stage is where things get nasty. If it has seen apps that are on its list, it will quietly extract the app's APK, modify it with malicious code, and then install that infected copy to replace the original clean one. It also uses a known exploit to bypass Android's own security system that checks exactly for such cases where an app was modified behind the scenes.
Agent Smith's infected apps then serve ads that do the usual phishing and scamming for financial gain. All at the literal expense of the user, of course. And since those users presumably installed the other apps from legitimate sources, they may be confident in presuming that those apps are operating normally.
The weakness of Agent Smith is prevention. Apps carrying the malware are often installed from third-party app stores offering unofficial or even pirated versions of some apps. There has been no reported sighting of the malware on Google Play Store and hopefully it will stay that way.