LastPass Authenticator Android app is easy to break into [Updated]
Password managers are supposedly the cure for the seemingly innate human tendency to use weak passwords. A special class of password managers take it a step further by using two-factor or two-step authentication or 2FA. But what is said authentication manager itself isn't as bulletproof as it should be? That is the rather odd situation that users of LastPass Authenticator on Android now find themselves in after it was revealed that it is almost trivial to get into the app and access the 2FA codes need, in turn, to get access to accounts and private data.
To be clear, it isn't the main LastPass password manager that's being deemed woefully insecure here. That one uses different security measures in order to make sure no one but you has access to your passwords. Measures that are, ironically, not applied to the LastPass Authenticator app on Android.
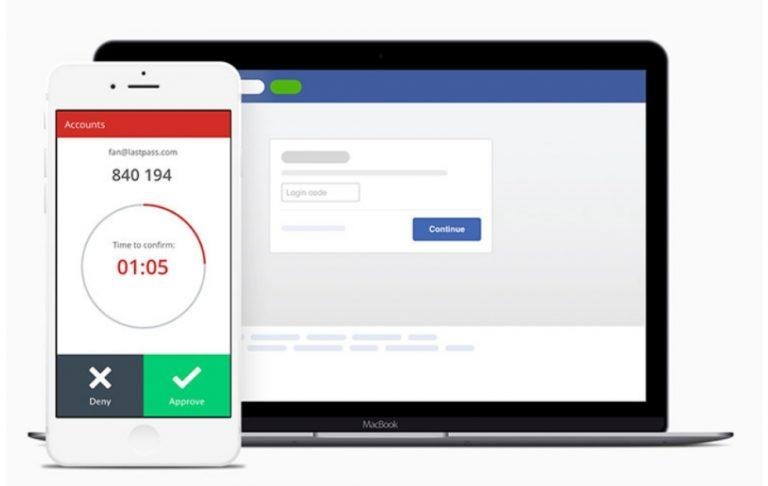
Like any Authenticator, the app works in lieu of sending an SMS to give the user a code to sign into an account. But according to dylan from Hacker Noon, it's virtually easy to get access to that code on Android. No root access required and no physical access even needed. The hacker simply need to get access to a specific activity or "page" of the app, which is unprotected by any sort of lock, PIN, or fingerprint authentication.
Granted, the circumstances that would lead to a remote access to the Authenticator may be a bit contrived. A malicious app must already be installed, waiting for the moment when the LastPass Authenticator is needed and then steal a 2FA code. Alternatively, the malware itself could attempt to log into some account and use LastPass Authenticator to get in.
Contrived or not, it isn't an excuse to leave any door open for such a critical piece of security software. dylan claims to have informed LastPass of the vulnerability way back in June and received confirmation that it was reproducible. LastPass has gone silent since then but now that it has gone public, it had no other choice but to say "we're working on it".
We're aware of the concern raised with the Authenticator app and are evaluating it thoroughly.
Users who continue to use strong passwords do not need to take any action at this time.— LastPass Support (@LastPassHelp) December 27, 2017
Update: LastPass says that it has addressed the issue: check out the full details.
VIA: Hacker Noon