First Chinese iOS Trojan Xsser mRAT targets Hong Kong activists
Protesters and activists these days have flocked to social media and mobile technology to circumvent censorship and blockades that prevent their message from reaching other people. But now the tables might have been turned on them. A new trojan malware called Xsser mRAT that infects iOS as well as Android devices has been discovered to be of Chinese origin and is seemingly targeting Hong Kong's Occupy Central movement.
Trojans or Trojan Horses are malware disguised as legitimate and useful software that creates a backdoor for unauthorized entities to access an infected system. These are nothing new, even on the iOS platform. However, this Xsser mRAT is notable because of its timing and its origin, leading Lacoon, the mobile security company that discovered this trojan, to label it as the first Andvanced Chinese Trojan for iOS. That said, the malware has first cropped up on Android and its origin and cross-platform nature has some rather worrying implications.
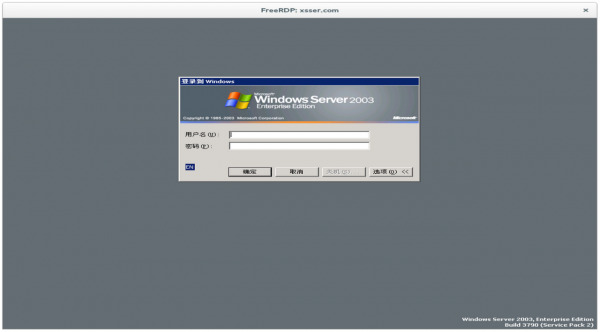
Lacoon has traced Xsser mRAT's CnC (Command and Control) domain to Chinese speaking attackers. Add in the fact that it is being spread via WhatsApp as a utility for helping the Occupy Central cause has led to theories that the trojan might be linked to the Chinese government's attempts to shutdown the protests and prosecute those involved. But since the Trojan doesn't discriminate Chinese from non-Chinese victims, Xsser mRAT's utility could be used for more far-reaching purposes, including spying on individuals, companies, or even governments.
The amount of information that the trojan can harvest is quite frightening. It can access smartphone messages, address books, call logs, media, and data from the popular Chinese messaging app Tencent. These are pretty much enough to give attackers an idea of the user's identity. It can also access GPS coordinates and even iOS account IDs, leading to a total compromise of the victim's privacy and security.
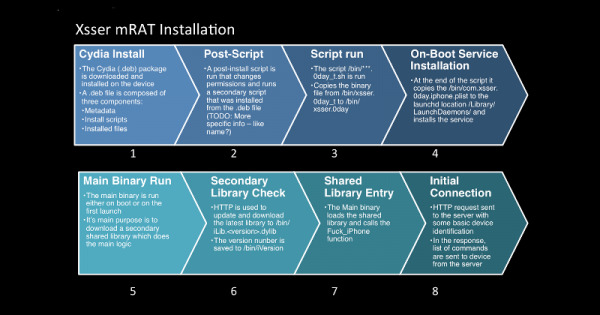
That said, at least for the iOS version of this trojan, a jailbroken iOS device is required, as the installation of Xsser mRAT starts with Cydia, the popular third party app store for jailbroken devices. Android users are not so lucky, as the malware can be easily installed if the user has enabled installing 3rd party software. That said, the whole process can really only be initiated if the user actually clicks on the WhatsApp message link and agrees to install the supposedly harmless but totally random app. Given the context of Occupy Central's protest against the Chinese government, that might not be a good idea in the first place.
SOURCE: Lacoon