WordPress Updates To Version 3.0.2 - Do It!
For everyone in the world who uses WordPress to blog their favorite technological news and gadgets, today you'll see a little update in your Dashboard by the name of 3.0.2. This update is what they call a mandatory security update, fixing a flaw that allowed evil Author-level users to get themselves a bunch more access than they were originally intended to, plus fixes a slew o' smaller bugs as well. As the blogging engine has evolved to the point where it basically updates itself, WordPress should be updated as often as it says it needs to – obey it!
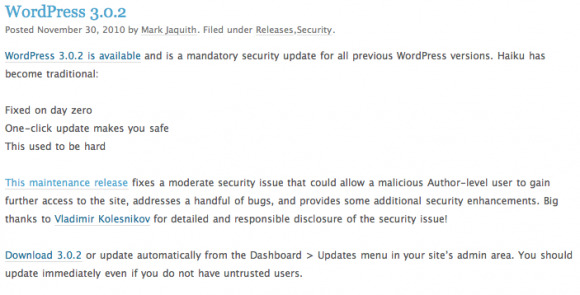
As this is a security update, I must appeal to you on a personal level to heed it, as my own personal blog has recently fallen victim to hacker attack, and all caution that can be taken should, especially when WordPress herself is appealing to your heart. Check out this update haiku as written by WordPress worker Mark Jaquith, written in hopes that you would update:
Fixed on day zero
One-click update makes you safe
This used to be hard
If you find yourself the victim of a hacker attack on your blog, as evidenced by your site suddenly being blocked by browsers, yelling, and ads popping up all over the place, I would also direct you to http://badwarebusters.org/ as they've more than once saved sites of your humble narrators from perilous troubles. Check out the full press release on this update below:
On November 30, 2010, WordPress 3.0.2 was released to the public. This is a mandatory security update for all previous WordPress versions.
For version 3.0.2, the database version (db_version in wp_options) remained at 15477.
Installation/Update Information
To download WordPress 3.0.2, update automatically from the Dashboard > Updates menu in your site's admin area or visithttp://wordpress.org/download/release-archive/.
Summary
▪ Fix moderate security issue where a malicious Author-level user could gain further access to the site. (r16625)
Other bugs and security hardening:
▪ Remove pingback/trackback blogroll whitelisting feature as it can easily be abused. (#13887)
▪ Fix canonical redirection for permalinks containing %category% with nested categories and paging. (#13471)
▪ Fix occasional irrelevant error messages on plugin activation. (#15062)
▪ Minor XSS fixes in request_filesystem_credentials() and when deleting a plugin. (r16367, r16373)
▪ Clarify the license in the readme (r15534)
▪ Multisite: Fix the delete_user meta capability (r15562)
▪ Multisite: Force current_user_can_for_blog() to run map_meta_cap() even for super admins (#15122)
▪ Multisite: Fix ms-files.php content type headers when requesting a URL with a query string (#14450)
▪ Multisite: Fix the usage of the SUBDOMAIN_INSTALL constant for upgraded WordPress MU installs (#14536)
List of Files Revised
wp-includes/ms-files.php
wp-includes/version.php
wp-includes/comment.php
wp-includes/functions.php
wp-includes/load.php
wp-includes/canonical.php
wp-includes/capabilities.php
readme.html
wp-admin/includes/plugin.php
wp-admin/includes/file.php
wp-admin/includes/update-core.php
wp-admin/plugins.php