What's a DDoS attack? Zombies, shopping help explain it all
There has been a lot of news today about DDoS; Feedly went down, and at the time we publish this article, still is. Those types of attacks happen often, and can cause some major headaches. What are they, though? Are you at risk if it happens? We explain DDoS in layman's terms to help you understand a bit about what's going on.
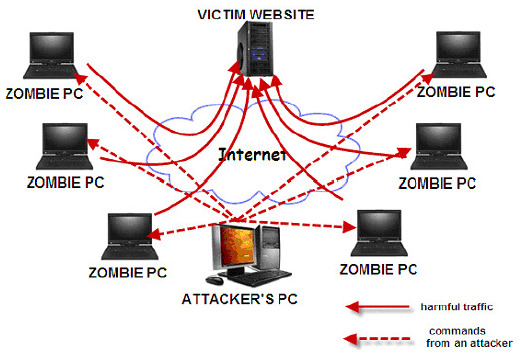
DDoS is an acronym for Distributed Denial of Service, which sounds as confusing as a series of letters. The "denial of service" is pretty straightforward (we don't get access to stuff), but what's with "distributed"? Typically, DDoS is a wide network of computers that occupy bandwidth to crash a server, so the attack is distributed in that instance.
When the network of computers contacts a specific website or server repeatedly, it causes slowdowns or, in the case of Feedly, a blackout. It's the digital equivalent to Black Friday shopping, where people get trampled in an attempt to get a limited number of popcorn machines from Wal-Mart.

So why do it? Several reasons, but two are overriding. The first involves information, where crashing a server means a rogue piece of code can be dropped without being noticed, compromising more than just the server (it could end up on our machines, keep reading for why that's bad). Aside from that, it could be a more involved information grab, with several bot computers attempting to break in at the same time.
The second reason is ransom. Sometimes, those attempting to crash a server simply want money, as was/is the case with Feedly. That doesn't mean they didn't drop nefarious code firecrackers, or do a smash-and-grab job for precious information. It just means they want someone to pay cold, hard cash ahead of them stopping — if they indeed do.
So are you at risk? Only if some black-hat hacker infected the server with malicious code that they can later access to turn your computer into one of their bots. That's typically why services choose to shut down rather than leave us with slowed access, because it's not really known what is going on until it's all said and done.
From US-CERT, the United States Computer Emergency Readiness Team (which falls under the Department of Homeland Security), we get a great rundown of why DDoS can end up badly for us:
In a distributed denial-of-service (DDoS) attack, an attacker may use your computer to attack another computer. By taking advantage of security vulnerabilities or weaknesses, an attacker could take control of your computer. He or she could then force your computer to send huge amounts of data to a website or send spam to particular email addresses. The attack is "distributed" because the attacker is using multiple computers, including yours, to launch the denial-of-service attack.
Like Zombies, once you're infected, you're part of the army. This is why many email providers limit the amount of messages coming and going on an account, and also why you shouldn't ever open those "Hey, I just made $7 million playing Bingo online!" emails. If you end up a bot, you could be used to for a future DDoS attack. DDoS may be a blunt instrument, but if your information is compromised, the method doesn't really matter, does it?
