NSA schemes mass internet infection and fake Facebooks
An NSA project to install spying malware on "millions" of computers around the world, dubbed TURBINE, could allow the clandestine US agency unprecedented access to "industrial-scale exploitation" in the battle for internet dominance. The spyware, which is said to have already been installed on as many as 100,000 systems after first being deployed in mid-2010, is described as both smart and aggressive, automating much of what would have previously needed a trained operative.
That, The Intercept's insiders say, makes it the perfect tool for broadly infecting a huge number of machines and casting a wide net for data collection. Rather than limit such actions to human operatives, TURBINE is an "intelligent command and control capability" that can run its own deployment and make its own decisions on which gathered data is important.
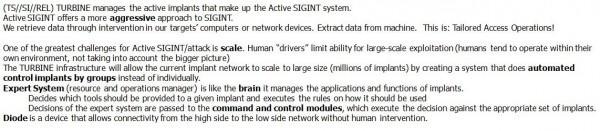
What makes TURBINE particularly interesting for the NSA is how little staff would have to know technically about infected systems and software in order to extract information.
The malware works to "relieve the user from needing to know/care about the details" an NSA document describes. The leaked file goes on to explain that TURBINE could be instructed to pull up all of the information about a certain application, and then would itself be responsible for figuring out the disparate places on the system that data was stored, where other related files might be, and which was most important to extract.
Part of the NSA's "Owning the Net" initiative, paid for with more than $67m in 2013, TURBINE works hand in hand with internet monitoring tools that are said to track when targets access sites the security agency is able to exploit. For instance, a fake Facebook server can be called into play by TURBINE in such a case, allowing the NSA to infect the remote computer.
Other approaches include clandestinely inserting a compromised server in-between regular network traffic, with the NSA using that "man-in-the-middle" positioning to log all data that passes through. Dubbed SECONDDATE, it can be used both for targeted attacks on specific systems, as well as to broadly disseminate malware.
TURBINE is allegedly supported by an array of remote "sensors" across multiple locations, which alert the command-and-control system to potential victims. That includes deployments at GCHQ-run monitoring stations in the UK, but potentially other places elsewhere in the world.
