Discovered Samsung Exynos Exploit Opens Door To Major Malware Problems
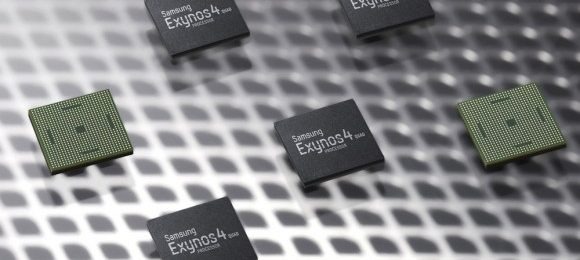
It isn't that often we get to write about an exploit that is both awesome and horrible at the same time, but today we're doing just that. A user over at the XDA Developers Forum has gone searching through Samsung Exynos kernels and has found one whopper of an exploit. This exploits affects a number of Samsung-made devices, along with potentially any device using an Exynos 4412 or 4210 processor and Samsung kernels, so a lot of Android users should be on the look out this evening.
Apparently, this exploit gives easy access to all of a device's RAM. This is pretty cool because it means that affected devices could be rooted extremely easily (we're talking one-click APK), but it's terrifying for exactly the same reason. With this exploit out in the open, it means that malicious apps could potentially root your device and take control just as easily, which is not a good thing at all.
Our friends at Android Community point out that this exploit affects multiple Galaxy S II models, the international Galaxy S III, and the Galaxy Note line up, so there are plenty of handsets floating around out there that could easily fall victim to malicious apps. Obviously, it's a good idea to only stick to downloading apps you trust while this exploit remains unfixed, otherwise you might open yourself up to a whole mess of problems.
Luckily, members of the XDA Developers Forum have alerted Samsung to the problem, and you can bet this is an exploit that the company will look to fix fast. If you want to use this exploit to easily root your device, member Chainfire has released a one-click APK you can use. While the ability to root your phone without a lot of work is pretty great, keep in mind that this is still a very dangerous exploit and that you should be vigilant when it comes to which apps you're downloading. We'll update you once Samsung says something about this exploit, so keep it tuned here to SlashGear for more!